In today's interconnected world, securely connect remote IoT P2P free has become an essential requirement for many tech enthusiasts and professionals. With the rise of IoT devices, ensuring secure communication between devices is paramount. Raspberry Pi, as a versatile and affordable platform, plays a crucial role in enabling users to establish secure peer-to-peer connections without incurring unnecessary costs.
As more individuals and businesses embrace the Internet of Things (IoT), the need for secure, reliable, and cost-effective solutions becomes increasingly important. Whether you're setting up a home automation system or building a professional-grade IoT network, establishing a secure P2P connection is critical to safeguarding your data.
This article provides an in-depth exploration of how to securely connect remote IoT devices using peer-to-peer (P2P) technology, focusing on the Raspberry Pi platform. By the end of this guide, you'll have the knowledge and tools to implement a secure and efficient IoT network that operates freely without compromising on security or performance.
Read also:The Fascinating World Of Homie A Comprehensive Exploration
Table of Contents
- Introduction to IoT P2P Connections
- Raspberry Pi: An Overview
- Why Secure Connections Matter
- Tools for Secure Connections
- Step-by-Step Guide to Secure Connections
- Optimizing Performance
- Security Best Practices
- Troubleshooting Tips
- Cost-Effective Solutions
- The Future of IoT P2P Connections
- Conclusion
Introduction to IoT P2P Connections
The Internet of Things (IoT) has revolutionized the way devices communicate and interact with one another. At the heart of this technology lies peer-to-peer (P2P) connectivity, which enables direct communication between devices without the need for a centralized server. This approach offers several advantages, including reduced latency, improved efficiency, and enhanced security.
Benefits of IoT P2P Connections
There are numerous benefits to using P2P connections in IoT applications:
- Decentralized Architecture: Eliminates the need for a central server, reducing dependency on third-party services.
- Improved Security: Direct connections minimize the risk of data breaches and unauthorized access.
- Cost-Effectiveness: Operating without intermediaries can significantly reduce operational costs.
By leveraging P2P technology, users can securely connect remote IoT devices, ensuring seamless communication and data transfer.
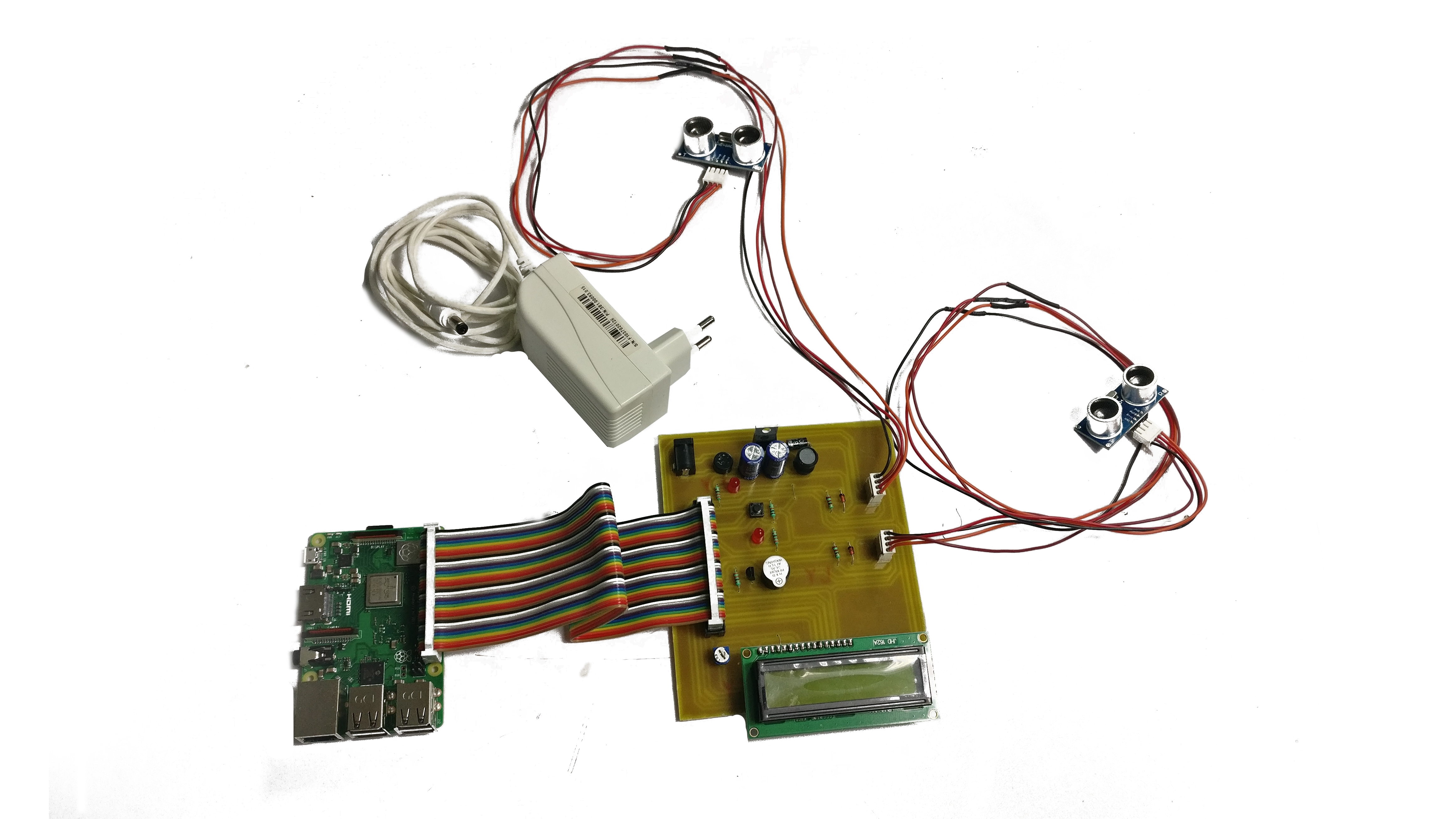
Raspberry Pi: An Overview
Raspberry Pi is a small, affordable computer that has gained immense popularity among developers, hobbyists, and educators. Its versatility and ease of use make it an ideal platform for IoT projects, enabling users to create innovative solutions with minimal resources.
Key Features of Raspberry Pi
Here are some of the standout features of Raspberry Pi:
- Compact Design: Ideal for embedded systems and portable applications.
- Open-Source Support: Access to a vast library of open-source software and resources.
- Community Support: A vibrant community of developers and enthusiasts contributing to its growth.
With its powerful hardware and software capabilities, Raspberry Pi serves as the perfect foundation for building secure IoT P2P connections.
Read also:The Comprehensive Guide To Understanding Rcs Messaging
Why Secure Connections Matter
In the realm of IoT, security is a top priority. As devices become increasingly interconnected, the risk of cyber threats and data breaches rises exponentially. Establishing secure connections is essential to protect sensitive information and maintain the integrity of IoT networks.
Common Security Threats in IoT
Some of the most common security threats in IoT include:
- Unauthorized Access: Hackers gaining access to devices and networks.
- Data Breaches: Leakage of sensitive information due to weak security protocols.
- DDoS Attacks: Distributed Denial of Service attacks overwhelming IoT devices.
By implementing robust security measures, users can mitigate these risks and ensure the safe operation of their IoT networks.
Tools for Secure Connections
To securely connect remote IoT devices using P2P technology, several tools and software solutions are available. These tools provide the necessary functionality to establish and maintain secure connections while ensuring optimal performance.
Popular Tools for IoT P2P
- WireGuard: A modern VPN solution that offers strong encryption and ease of use.
- Tailscale: A zero-config mesh network solution designed for secure P2P connections.
- OpenVPN: A widely-used open-source VPN protocol with robust security features.
These tools, combined with the capabilities of Raspberry Pi, enable users to create secure and efficient IoT networks.
Step-by-Step Guide to Secure Connections
Setting up a secure IoT P2P connection using Raspberry Pi involves several key steps. Below is a comprehensive guide to help you get started:
Step 1: Install Raspberry Pi OS
Begin by installing the latest version of Raspberry Pi OS on your device. This operating system provides the necessary tools and libraries to support IoT applications.
Step 2: Configure Network Settings
Configure your Raspberry Pi's network settings to ensure proper connectivity. This includes setting up static IP addresses and enabling SSH for remote access.
Step 3: Install Security Software
Install a reliable security tool, such as WireGuard or OpenVPN, to establish secure P2P connections. Follow the official documentation for installation and configuration instructions.
Step 4: Test the Connection
Once everything is set up, test the connection to ensure secure and stable communication between devices.
Optimizing Performance
Optimizing the performance of your IoT network is crucial for ensuring smooth operation and minimizing latency. Here are some tips to enhance the performance of your Raspberry Pi-based IoT setup:
Performance Optimization Tips
- Use Efficient Protocols: Opt for lightweight communication protocols to reduce bandwidth usage.
- Implement Caching: Cache frequently accessed data to improve response times.
- Monitor Resource Usage: Regularly monitor CPU, memory, and disk usage to identify potential bottlenecks.
By following these optimization strategies, you can maximize the efficiency of your IoT network.
Security Best Practices
Adhering to security best practices is essential for maintaining the safety and integrity of your IoT network. Below are some recommended practices to enhance security:
Best Practices for IoT Security
- Regular Updates: Keep your software and firmware up to date to patch vulnerabilities.
- Strong Authentication: Use strong passwords and multi-factor authentication to secure access.
- Network Segmentation: Segment your network to isolate IoT devices from other systems.
Implementing these practices will help safeguard your IoT network against potential threats.
Troubleshooting Tips
Encountering issues while setting up your IoT P2P connection is not uncommon. Below are some troubleshooting tips to help you resolve common problems:
Common Issues and Solutions
- Connection Failures: Check network settings and ensure all devices are properly configured.
- Security Alerts: Review security logs to identify and address potential threats.
- Performance Issues: Optimize resource usage and consider upgrading hardware if necessary.
By following these troubleshooting steps, you can quickly identify and resolve issues in your IoT network.
Cost-Effective Solutions
One of the key advantages of using Raspberry Pi for IoT applications is its cost-effectiveness. By leveraging open-source software and affordable hardware, users can create secure IoT P2P connections without breaking the bank.
Cost-Saving Strategies
- Open-Source Software: Utilize free and open-source tools to reduce software costs.
- Energy Efficiency: Optimize power consumption to lower operational expenses.
- DIY Solutions: Build custom solutions tailored to your specific needs.
These strategies enable users to implement secure and cost-effective IoT solutions.
The Future of IoT P2P Connections
As technology continues to evolve, the future of IoT P2P connections looks promising. Advancements in encryption, networking, and hardware capabilities will further enhance the security and performance of IoT networks.
Emerging Trends in IoT
- 5G Connectivity: Faster and more reliable connections for IoT devices.
- Edge Computing: Processing data closer to the source for improved efficiency.
- AI Integration: Enhanced decision-making through artificial intelligence.
These trends will shape the future of IoT and pave the way for innovative applications and solutions.
Conclusion
In conclusion, securely connect remote IoT P2P free using Raspberry Pi is not only achievable but also highly beneficial. By following the steps and best practices outlined in this guide, you can create a secure and efficient IoT network that meets your specific needs.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies. Together, let's build a safer and more connected world!