In today's digital age, securely connect remote IoT P2P on Raspberry Pi for free is a growing necessity for tech enthusiasts and professionals alike. The Internet of Things (IoT) has revolutionized how we interact with devices, making it essential to understand the secure methods of remote connectivity. Whether you're managing smart home systems or industrial automation, ensuring secure connections is paramount.
As IoT continues to expand, so does the need for robust security measures. This article will provide you with a detailed guide on how to set up a secure peer-to-peer (P2P) connection for your IoT devices using a Raspberry Pi without spending a dime. We'll explore the tools, techniques, and best practices to safeguard your devices from potential threats.
By the end of this article, you'll have a clear understanding of the steps required to create a secure remote IoT P2P connection using Raspberry Pi. Let's dive in and explore the possibilities of enhancing your IoT network's security.
Read also:A Comprehensive Journey From Kansas City Mo To Omaha Ne A Travelers Guide
Table of Contents
- Introduction to IoT Security
- Understanding Raspberry Pi Basics
- Why Securely Connect Remote IoT P2P?
- Tools and Software Needed
- Setting Up the Raspberry Pi
- Methods for Secure Connections
- Troubleshooting Common Issues
- Optimizing Security for IoT Devices
- Benefits of a Secure IoT P2P Connection
- Conclusion and Next Steps
Introduction to IoT Security
IoT security is a critical aspect of modern technology. As more devices become interconnected, the risk of unauthorized access and data breaches increases. A secure connection ensures that your IoT devices remain protected from malicious actors.
When you securely connect remote IoT P2P on Raspberry Pi for free, you're taking a proactive step toward safeguarding your network. This section will delve into the importance of IoT security and its implications for both personal and professional use cases.
Understanding the basics of IoT security will help you appreciate the significance of implementing secure protocols. By following best practices, you can ensure that your devices remain safe and functional.
Understanding Raspberry Pi Basics
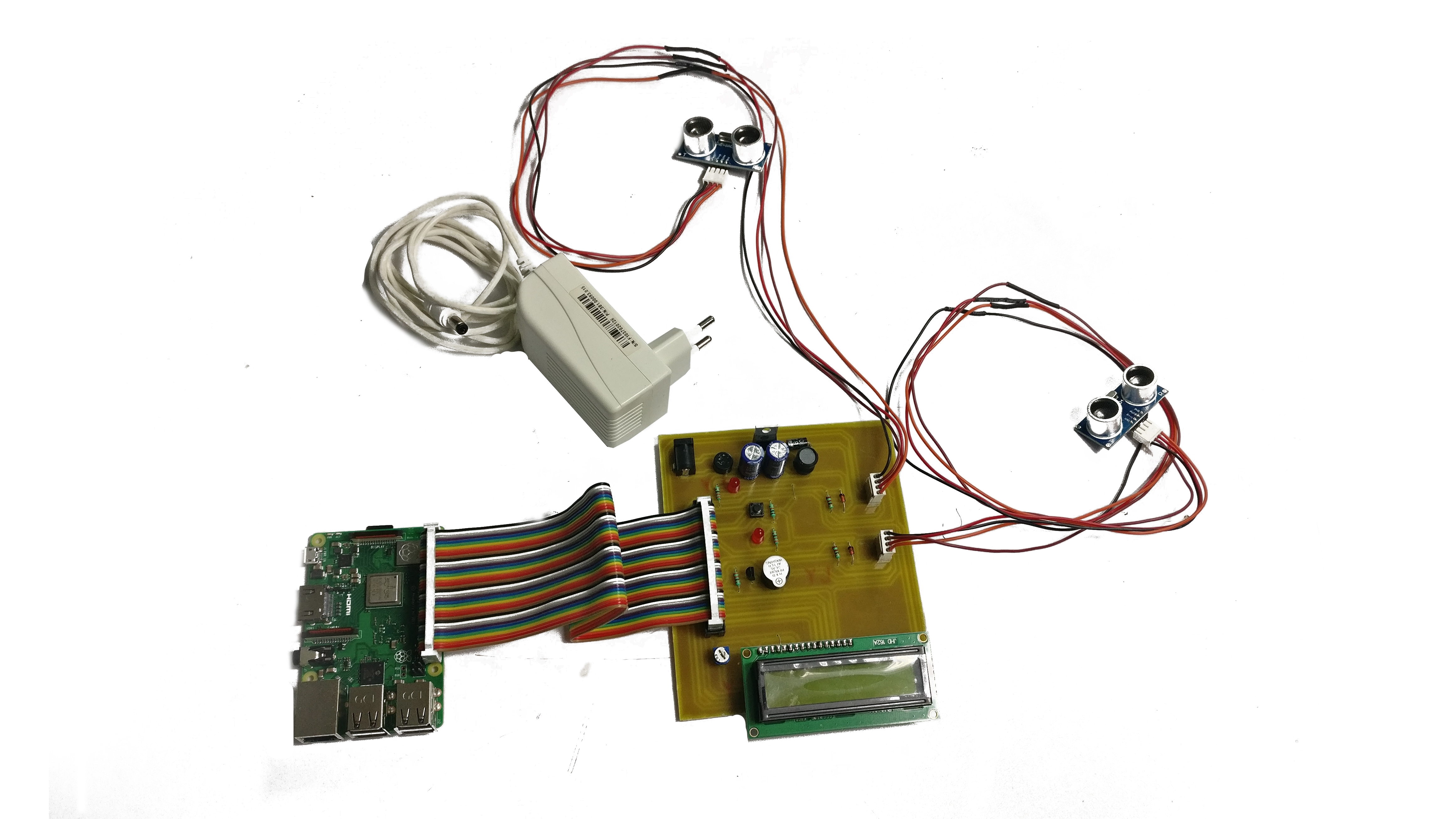
The Raspberry Pi is a versatile single-board computer that has gained popularity among hobbyists and professionals. Its affordability and flexibility make it an ideal choice for setting up secure IoT P2P connections.
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for multiple operating systems
- Compatibility with various sensors and modules
Before proceeding, it's essential to familiarize yourself with the Raspberry Pi's capabilities and limitations. This knowledge will help you optimize its performance for your IoT projects.
Why Securely Connect Remote IoT P2P?
Securing your IoT devices is crucial for maintaining privacy and protecting sensitive data. A remote IoT P2P connection allows you to manage your devices from anywhere in the world, provided the connection is secure.
Read also:Spooktacular Halloween Decorations Transform Your Space With Creativity And Charm
Risks of Insecure Connections
- Data breaches
- Unauthorized access
- Device hijacking
By securely connecting remote IoT P2P on Raspberry Pi for free, you can mitigate these risks and ensure the integrity of your network. This section will highlight the potential dangers of insecure connections and emphasize the importance of security measures.
Tools and Software Needed
To set up a secure IoT P2P connection using Raspberry Pi, you'll need the following tools and software:
- Raspberry Pi board
- Power supply and microSD card
- SSH client (e.g., PuTTY)
- Operating system (e.g., Raspberry Pi OS)
Additionally, you may require specific libraries and packages depending on your project requirements. This section will guide you through the necessary setup steps and provide links to download the required software.
Setting Up the Raspberry Pi
The initial setup of your Raspberry Pi involves installing the operating system and configuring basic settings. Follow these steps to prepare your device for secure IoT P2P connectivity:
Step 1: Install the Operating System
Download the Raspberry Pi OS image and write it to your microSD card using a tool like Balena Etcher. Ensure that the installation process is error-free before proceeding.
Step 2: Configure Network Settings
Set up Wi-Fi or Ethernet connectivity on your Raspberry Pi. This step is crucial for enabling remote access to your device.
By following these steps, you'll have a functional Raspberry Pi ready for secure IoT P2P connections.
Methods for Secure Connections
There are several methods to securely connect remote IoT P2P on Raspberry Pi for free. Below are some of the most effective techniques:
SSH Tunneling
SSH tunneling provides a secure channel for data transfer between devices. It encrypts all communication, ensuring that your IoT devices remain protected from eavesdropping.
VPN Configuration
Setting up a virtual private network (VPN) on your Raspberry Pi adds an extra layer of security to your IoT network. This method is particularly useful for managing devices across different locations.
Both methods have their advantages and can be combined for enhanced security. This section will provide detailed instructions for implementing these techniques.
Troubleshooting Common Issues
Even with the best preparation, issues may arise during the setup process. Here are some common problems and their solutions:
- Connection Errors: Verify network settings and ensure that all devices are properly connected.
- Authentication Failures: Check SSH keys and user credentials to resolve authentication issues.
- Performance Issues: Optimize your Raspberry Pi's configuration to improve performance.
By addressing these issues promptly, you can ensure a smooth setup process and minimize downtime.
Optimizing Security for IoT Devices
Securing your IoT devices goes beyond just setting up a connection. Regular maintenance and updates are essential for maintaining a secure network.
Best Practices for IoT Security
- Regularly update firmware and software
- Use strong passwords and two-factor authentication
- Monitor network activity for suspicious behavior
Implementing these best practices will help you maintain a secure IoT environment and protect your devices from potential threats.
Benefits of a Secure IoT P2P Connection
Setting up a secure IoT P2P connection using Raspberry Pi offers numerous benefits, including:
- Enhanced security for your devices
- Remote management capabilities
- Cost-effective solution for IoT projects
By leveraging the power of Raspberry Pi, you can create a robust and secure IoT network that meets your needs.
Conclusion and Next Steps
In conclusion, securely connect remote IoT P2P on Raspberry Pi for free is a valuable skill for anyone involved in IoT projects. By following the steps outlined in this article, you can ensure that your devices remain protected from potential threats.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT and related technologies.
Thank you for reading, and happy tinkering!
Data Source: Raspberry Pi Foundation, SSH.COM, OpenVPN